Less Tech Noise. More Strategic Insights
Join 5000+ Tech leaders & CISOs receiving our deep-dive insights.
API VAPT Testing Framework: A Step-by-Step Guide for Enterprise Security Teams
Businesses treat APIs like growth engines. Attackers treat them like unlocked doors.
The gap between those two realities is where most enterprise security programs have a blind spot.
Many APIs are pushed live like a cashier approving transactions during rush hour, fast, automated, and without checking payment authenticity. That question is where API security debt begins to accumulate.
The goal of a structured API VAPT testing framework is to ensure that the question never needs to be asked, because the answer is already built into how your team operates.
This blueprint walks enterprise security teams through a six-step API VAPT workflow — from scoping and methodology selection to CI/CD integration and continuous coverage.
Own API (VAPT) vs Third-party API (Pentest)
Before the steps begin, one scoping decision shapes everything else: are you testing your own APIs, or third-party APIs your systems consume?
For your own APIs, VAPT, vulnerability assessment, followed by penetration testing, provides comprehensive coverage of how your endpoints are built, authenticated, and exposed. For third-party APIs, penetration testing is typically the more appropriate scope, focused on how that surface interacts with your environment.
This distinction determines your methodology, your tooling, and what a successful outcome looks like. Get it wrong up front, and the entire engagement yields findings that don’t match the risk you actually care about.
If your team is still building foundational API security visibility, start with our guide on API VAPT explained and how to secure endpoints from data leaks before implementing a full enterprise testing framework.
The step-by-step framework
Step 1: Compliance or Security Posture? Define Your Objective Before Testing Begins
Most API VAPT engagements fail to produce useful outcomes, not because of bad testing, but because of a vague mandate.
“Test our APIs” is not an objective. Before a single request is intercepted, your team needs a clear answer to one question: what are we trying to learn?
There are two legitimate business drivers, each requiring a different approach.
- Compliance-driven VAPT is scoped to adhere to PCI DSS, ISO 27001, HIPAA, or SOC 2. This report is primarily for auditors; the testing methodology is standard, and the scope is limited to what the frameworks mandate.
- Security posture-driven VAPT, this is where you actually understand the risk. This audit’s sole goal is to determine what an attacker would discover if they targeted your APIs today. The scope is broader, the methodology is more adversarial, and the findings feed directly into your development backlog.
For most enterprise teams operating in a continuous delivery environment, security posture is the primary objective. Compliance becomes a natural byproduct, not the reason you test.
Step 2: Scope the Engagement (What Exactly Gets Tested?)
Scope definition is where enterprise API VAPT engagements most commonly go wrong. During API testing, the teams either test too broadly, getting surface-level results, or too narrowly, missing entire service chains.
A well-scoped API VAPT engagement for an enterprise team should answer the following before testing begins:
- Which APIs are in scope? List all candidates: internal APIs, customer-facing APIs, partner-integrated APIs, legacy or undocumented endpoints, and shadow APIs—which are often exploited and should be clearly included or excluded.
- What environments will be tested? Staging allows aggressive testing without production risk. However, some vulnerabilities, especially related to rate limiting, session management, and real-time transactions, can only be accurately assessed in production with proper safeguards and rollback procedures.
- What API types are in scope? REST, GraphQL, SOAP, and WebSocket APIs each carry distinct vulnerability profiles. GraphQL in particular requires specific attention to introspection, query depth limits, and field-level authorization — areas that standard REST-focused tools handle poorly.
- What authentication mechanisms are in use? OAuth 2.0, JWT, API keys, SSO integrations, and session tokens all need to be explicitly documented. Each introduces its own testing requirements.
- What is explicitly out of scope? Defining boundaries is as important as defining targets. Document exclusions clearly to avoid scope creep and protect production systems.
To speed up scoping, we’ve built a free API VAPT checklist — with exact How-to-Test instructions for each. Download it here
Step 3: Select Your Testing Framework (OWASP, NIST, or PTES?)
The framework you choose determines the depth of your coverage, the structure of your findings, and the vocabulary your remediation teams use to prioritize fixes.
The three frameworks most commonly applied to enterprise API VAPT engagements are:
- OWASP API Security Top 10 is the most widely adopted reference for API-specific vulnerabilities. It maps the ten most critical API risks.
- NIST SP 800-115 provides a more structured, process-oriented testing methodology — reconnaissance, discovery, attack execution, and reporting. Ideal for teams needing security testing for federal requirements or building a repeatable internal process.
- PTES (Penetration Testing Execution Standard) offers the most comprehensive adversarial framework, structured around pre-engagement, intelligence gathering, threat modeling, exploitation, post-exploitation, and reporting. It is the preferred choice for red team API VAPT, simulating real attacks rather than relying on checklists.
The best approach for the DevSecOps teams is to use a combination of these frameworks. OWASP API Top 10 as the vulnerability taxonomy, NIST SP 800-115 as the process structure, and PTES for high-value engagements.
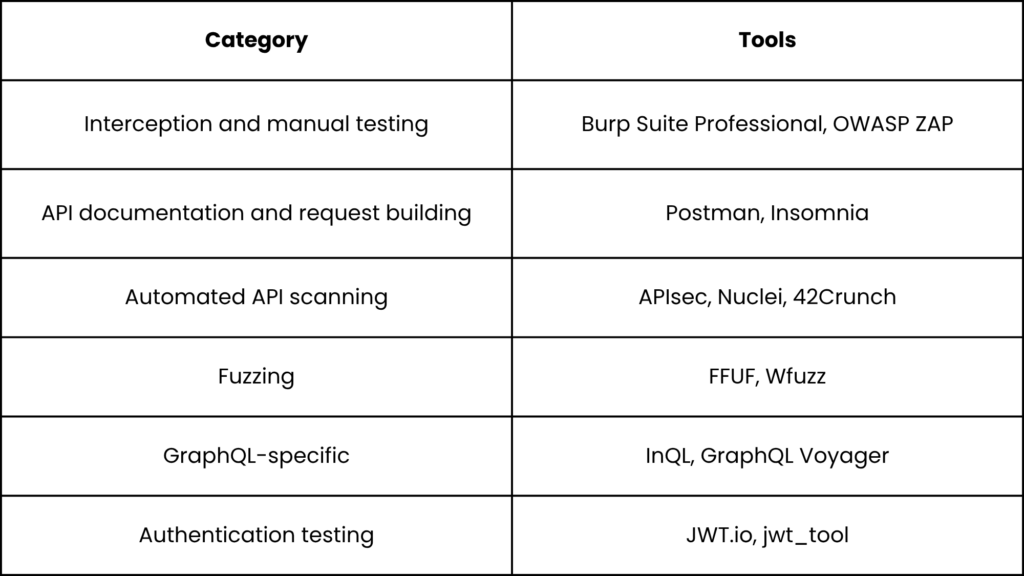
Step 4: Execute the Testing (Parameters, Tools, and the CI/CD Integration Point)
- Authentication and Token Security
Every API VAPT engagement starts here.
- Test for JWT manipulation algorithm confusion attacks (switching from RS256 to HS256)
- expired token acceptance
- missing signature validation
- token reuse after logout.
For OAuth 2.0 implementations,
- test authorization code interception
- PKCE enforcement
- redirect URI validation.
For API keys,
- assess key rotation policies,
- transmission security,
- and whether keys are inadvertently exposed in logs, error messages, or version control.
- Object-Level and Function-Level Authorization (BOLA and BFLA)
BOLA (Broken Object Level Authorization) is ranked the number one API security risk for good reason. It occurs when an API exposes object identifiers (user IDs, order numbers, document references) in requests without verifying that the requesting user has access to that specific object.
Testing requires creating multiple user accounts at different privilege levels and systematically substituting object identifiers across requests. Automated scanners consistently miss this because it requires understanding business context, not just pattern matching.
- Input Validation — Injection, Fuzzing, and Parameter Tampering
Test all input surfaces for SQL injection, NoSQL injection, XML injection, and command injection. Apply fuzzing to parameter values, headers, and request bodies to identify unexpected behaviors such as:
- crashes
- verbose error messages
- stack traces
- partial data returns.
Parameter tampering, manipulating data types, boundary values, and unexpected formats can reveal both technical vulnerabilities and business logic flaws. These issues often go undetected by injection testing alone.
- Rate Limiting and Resource Consumption
Test whether endpoints enforce rate limits consistently across authenticated and unauthenticated requests. Absent or inconsistent rate limiting enables credential stuffing, brute force attacks, and denial-of-service conditions. In enterprise environments, resource consumption vulnerabilities are frequently found in batch endpoints, export functions, and search APIs where no throttling exists because the original developer assumed only internal callers would use them.
- Business Logic Flaws
This is the category that automated tools cannot test. Business logic flaws are vulnerabilities that exist in the intended workflow of an API, not in the underlying code. Examples include: placing an order with a negative quantity to generate a credit, skipping steps in a multi-step verification flow, manipulating transaction states, or accessing another user’s data by modifying a parameter that should be server-enforced. Testing business logic requires testers who understand what the API is supposed to do and systematically attempt to make it do something it isn’t supposed to.
- The CI/CD Integration Point
- On every pull request: Automated DAST scans for OWASP API Top 10 categories against a staging instance. Fast, lightweight, blocks critical findings from merging.
- On every main branch merge: Broader automated scan including authentication flows, rate limit checks, and response schema validation.
- Nightly scheduled runs: Full regression suite against the staging environment, including fuzzing and injection tests.
- Manual VAPT engagement: Quarterly or after significant architectural changes — covering business logic, complex authorization chains, and anything that automated tools are structurally unable to detect.
This model maintains continuous security without making every commit a blocker. Manual VAPT does not replace pipeline scanning — it covers what pipeline scanning cannot reach.
Step 5: Define What Good Output Looks Like
The quality of a VAPT engagement is ultimately judged by the quality of its output.
Every finding in a high-quality API VAPT report should contain:
- Vulnerability classification mapped to OWASP API Top 10 or CVSS score
- Affected endpoint(s) with full request and response evidence
- Reproduction steps — a developer should be able to replicate it without further conversation
- Business impact statement — not just technical risk, but what an attacker could achieve
- Remediation guidance — specific to your stack, not generic advice
- Severity rating — Critical, High, Medium, Low, Informational — with clear criteria for each
Define remediation criteria before testing begins. Agree on what constitutes an acceptable risk threshold, which findings must be fixed before the next release, which can be tracked in the backlog, and which are accepted risks with documented rationale.
Step 6: Retest, Close the Loop, and Build Continuous Coverage
VAPT is not a one-and-done security ritual. Threats evolve daily, and so should your testing.
After remediation, every finding rated High or Critical must be retested against the fix.
Developers may fix specific cases but leave vulnerabilities open through other means. Independent retesting identifies these issues and provides a verified closure record essential for compliance and stakeholder trust.
For long-term continuous coverage, enterprise teams should maintain the following:
- An API inventory: Maintain a continuously updated API inventory to identify and secure undocumented or “zombie” endpoints before attackers exploit them.
- A VAPT cadence: Align VAPT frequency with release velocity using continuous scanning and regular manual assessments to catch security regressions early.
- A feedback loop into development: Turn VAPT findings into secure coding improvements by fixing root-cause issues instead of repeatedly patching symptoms.
This is what transforms API VAPT from a compliance activity into a genuine security posture improvement program.
How Infosprint Technologies Runs API VAPT for Enterprise Teams
Running a credible API VAPT engagement requires methodology independence — which is exactly what an external assessment provides.
At Infosprint Technologies, we combine manual testing depth with automated coverage, built around the same OWASP, NIST, and PTES frameworks this guide is structured around. Generating findings that engineering and leadership teams can actually act on.
Our process includes:
- Deep endpoint analysis mapped to both OWASP and NIST frameworks
- Token and authentication testing across OAuth 2.0, JWT, and SSO integrations
- Parameter tampering, fuzzing, and injection validation across REST and GraphQL surfaces
- Detailed reporting with CVSS-rated findings, reproduction evidence, and stack-specific remediation guidance
Every engagement closes with a retest cycle to verify that reported vulnerabilities have been effectively resolved, not just acknowledged.
Download the Infosprint’s:
API VAPT checklist
VAPT assessment template
which you can use to run internal reviews or brief a security vendor.
Our goal is to help your organization stay resilient, compliant, and breach-free — while enabling your developers to deploy secure APIs faster, not slower.
If you’re ready to run a structured API VAPT engagement for your enterprise environment, or want to understand what scope and methodology make sense for your specific API stack, Get in touch with our security team.
Frequently Asked Questions
Start by inventorying all API endpoints, including shadow and legacy ones. Then run automated DAST scans for surface-level issues and manual testing for authentication flaws, authorization logic, and business logic vulnerabilities. Map findings against the OWASP API Security Top 10. Automated tools give breadth; manual testing gives depth. Both are required for a credible enterprise assessment.
A structured API pen test follows five stages:
- scope definition
- Framework selection
- test execution across authentication
- Authorization
- input validation
- business logic
Findings documentation with severity ratings and reproduction steps, and a retest cycle to verify remediation. For enterprise teams, each stage requires sign-off from security and engineering leads before the next begins.
Define your testing objective first: compliance or security posture. Then establish a scope template, select your framework (OWASP, NIST, or PTES), document your parameter checklist, integrate automated scanning into your CI/CD pipeline, and set a cadence for manual engagements. The framework is operational only when remediation criteria and retest protocols are defined.
In-house works if your security team has dedicated API testing expertise, the right toolset, and the capacity to test without conflicts of interest. Most enterprise teams consistently lack all three. A vendor brings methodology independence, specialist tooling, and objective findings that carry more weight with auditors and leadership. Many teams use a hybrid approach: internal automated scanning and external manual VAPT.
Run lightweight automated DAST scans on every pull request against a staging instance. Expand to include broader authentication and rate-limit checks on main branch merges. Schedule nightly full regression runs, including fuzzing. Reserve manual VAPT for quarterly engagements or post-major-release cycles. The goal is continuous coverage for known vulnerability patterns, with human judgment layered on top for complex logic flaws.
Related Blogs

Missiles, Models & a Pentagon Deal: March 2026
How Retailers Reduce Costs by 40–60% While Improving Customer Experience




