
Less Tech Noise. More Strategic Insights
Join 5000+ Tech leaders & CISOs receiving our deep-dive insights.
Canadian Business Cybersecurity Playbook: A 7-Step Framework for 2026
Most Canadian business owners treat cybersecurity like their car’s spare tire: something you only think about when things go wrong.
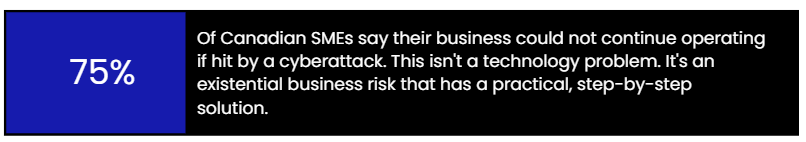
That approach is costing Canadian businesses hundreds of millions of dollars a year. But unlike a flat tire on the highway, a cyberattack doesn’t give you a dashboard warning light. By the time you realize something is wrong, the damage is already happening.
That assumption is exactly what attackers count on.
73% of Canadian small and medium-sized businesses have experienced a cybersecurity incident. Most didn’t think they were targets — until they were.
At Infosprint Technologies, we help Canadian organizations facing these exact challenges. This guide reflects that experience, a practical, step-by-step approach to building security that fits the realities of growing businesses.
By the end, you’ll be able to answer a critical question:
What does a defensible cybersecurity posture actually look like for a company like ours?
“Cybersecurity isn’t a technology problem. It’s a business continuity problem, and every Canadian business owner needs to treat it like one.” – Muppala Chandra Sekhar Reddy, Sr. manager Cybersecurity
What Makes Canada Uniquely Exposed?
Cybersecurity advice written for a global audience often misses what makes Canada’s environment unique: regulatory expectations, economic ties, and the specific threats targeting Canadian organizations.
Canada’s National Cyber Threat Assessment (2025–2026) identifies three dominant risks:
- Ransomware-as-a-service operations targeting small and mid-sized organizations
- State-sponsored espionage targeting Canadian intellectual property
- AI-enabled social engineering and phishing attacks
The financial stakes are significant. The average cost of a data breach in Canada reached CA$6.98 million in 2025, ranking among the highest globally.
Legal obligations add another layer. Federal privacy law PIPEDA, alongside provincial frameworks in Alberta and British Columbia, requires organizations to disclose breaches that actually carry a serious risk of harm. Many US-focused cybersecurity guides fail to address these requirements accurately.
Meanwhile, Canada’s digital economy increasingly connects SMBs to US supply chains. That integration makes Canadian firms attractive “side-door” entry points into larger enterprises.
Recent studies reinforce the urgency:
- Over 70% of Canadian SMBs experienced a cyberattack in 2024 (KPMG)
- Two-thirds of ransomware victims paid the ransom
- The Canadian government has committed over $900 million to strengthen national cybersecurity, but individual businesses remain responsible for their own defenses
“Clients and insurance are asking us about Information Security, but we don’t know where to start.”
- A common statement heard from business owners.
Security Is Not a Checkbox. It’s a Posture
Most cybersecurity advice focuses on a checklist – Install antivirus | Enable MFA | Train employees. Those steps matter — but they’re incomplete.
A checklist gives you compliance. A posture gives you resilience.
This distinction matters because today’s threat landscape doesn’t reward box-ticking. Ransomware operators run automated scans across thousands of organizations daily, searching for a single misconfigured system or compromised credential.
The companies that recover fastest from attacks aren’t the ones with the most tools. They are the ones with:
- A clear security philosophy
- Consistent practices
- Tested recovery procedures
- Leadership alignment around risk
Cybersecurity isn’t an IT task. It’s an operational discipline that protects revenue, trust, and long-term growth. Organizations that treat cybersecurity as a business discipline are better positioned to manage risk and scale securely.
“Security isn’t about adopting every framework. It’s about understanding your exposure and building protections that fit how your business actually operates.” Muppala Chandra Sekhar Reddy, Sr. Manager Cybersecurity
The 7 Step Framework to Building a Canadian Cybersecurity Posture
The following framework is designed to be practical for organizations with 5 – 250 employees, not enterprise security theatre, not a $500,000 CISO engagement. Each step builds on the last. You don’t have to do everything at once. You do have to start somewhere.
STEP 1: Know What You’re Protecting (Asset & Data Inventory)
The most common entry point for a cyberattack isn’t a sophisticated zero-day exploit or a state-sponsored hacking team. It’s a cloud tool your finance team signed up for eighteen months ago that nobody remembers, sitting with read/write access to your customer database.
“The first risk we uncover is often forgotten data — information stored, shared, and accessible long after the business stopped thinking about it.” – Infosprint POV
You cannot protect what you haven’t mapped. Before a single security tool is deployed or a single policy is written, every Canadian business needs a clear, honest answer to three questions:
- Where does your customer and employee data actually live?
- Which systems and tools are accessible from the public internet?
- Which third-party applications and vendors have access to sensitive information?
This isn’t a technology exercise. It’s a business exercise that requires a spreadsheet, a few hours, and involvement from every team that touches data — not just IT.
What to map in your inventory:
- Devices: Laptops, desktops, phones, tablets — company-owned and personal devices used for work.
- Software and SaaS tools: Every application your team logs into, including free-tier tools. Pay special attention to tools that sync with email or cloud storage.
- Data types and locations: Where does customer personal information live? Financial records? Employee data? Is it in one place or scattered across five different platforms?
- Third-party access: Which vendors, contractors, or integrations have access to your systems? What level of access do they have?
- Internet-facing systems: Your website, customer portals, remote access tools, and any APIs are all potential entry points that need to be accounted for.
In Canada, this step isn’t just good practice — it has legal weight. Under PIPEDA, organizations must be able to identify when personal information has been breached and assess whether that breach poses a “real risk of significant harm” to the individuals affected. You can’t make that determination if you don’t know what data you hold or where it is.
STEP 2: Assess Your Risk, Not Your Fear (Threat & vulnerability)
Risk assessment sounds like something that belongs in a 200-page consulting report. It doesn’t. At the SMB level, it means sitting down and honestly answering two questions: What is most likely to happen to us? And what would hurt us most if it did?
Most small businesses make the mistake of trying to protect against everything at once, which means they end up protecting nothing particularly well. Risk assessment is the discipline of knowing where to focus first.
The threats most likely to hit a Canadian SMB in 2025:
- Phishing via business mail: The entry point for most attacks. According to BDC, 61% of Canadian small businesses have received phishing attempts.
- Weak or Stolen Credentials: Compromised usernames and passwords from data breaches on other platforms are constantly sold and traded. If your employees reuse passwords, and statistically, many of them do, you’re one leaked credential database away from a breach.
- Unpatched Software: Software updates exist because vulnerabilities were found. Every day an update goes uninstalled is a day attackers can exploit a known flaw in your system.
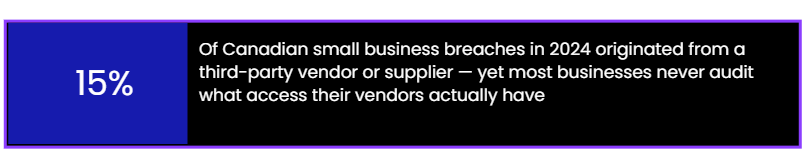
- Third-Party and Supply Chain Risk: You’re only as secure as the least secure organization with access to your systems.
- Ransomware: Canada now has the 4th-highest rate of ransomware incidents globally. Once ransomware is deployed, your choices are pay the ransom, restore from backup, or lose your data. Two of those three outcomes require significant preparation before the attack happens.
Building a simple risk matrix:
You don’t need specialized software to do this. A simple two-axis scoring system works: rate each risk by likelihood (low, medium, high) and impact (low, medium, high). Your highest-priority risks are those that score high on both axes. Start there. Not everywhere at once.
STEP 3: Lock Down Identity (The New Security Parameter)
The old model of network security was simple: build a wall, keep threats outside, trust everything inside. That model is obsolete. Your systems don’t have walls anymore. They have login pages.
Cloud platforms, remote work, SaaS tools, and mobile devices have dissolved the traditional network perimeter. Today, your ‘perimeter’ is every user identity — every username and password that can open a door to your systems. Identity is the new perimeter. And most Canadian SMBs have left it wide open.
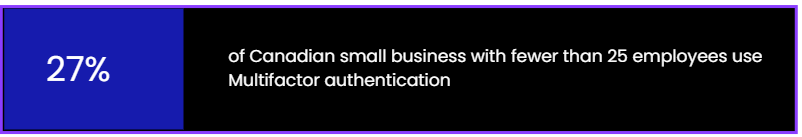
- MFA everywhere: Email is the master key to most of your other accounts — protect it first. Then, cloud storage, finance tools, CRM, and any remote access systems.
- Password manager: Strong, unique passwords for every system are impossible to maintain without a tool. Business-grade password managers (1Password Teams, Bitwarden for Business) solve this for the entire organization.
- Principle of least privilege: Every employee and every system integration should have access only to what they specifically need — nothing more. An accounts payable clerk doesn’t need access to your customer database. A marketing tool doesn’t need access to your financial systems.
- Quarterly access reviews: Regularly audit who has access to what. Remove access immediately when an employee leaves — not at the end of the week, not when IT gets around to it. Immediately.
- Single Sign-On (SSO): For businesses using five or more cloud applications, SSO centralizes authentication, streamlines access control and facilitates the implementation of uniform security policies.
“In Canada, 15–20% of user credentials are at risk of compromise due to reuse, weak passwords, or prolonged access. The greater risk arises when those accounts lack MFA and appropriate access controls”. Muppala Chandra Sekhar Reddy, Sr. Manager Cybersecurity
STEP 4: Protect Your Endpoints & Email (where Actually Land)
Email remains the most common attack vector worldwide. Not because it’s the most sophisticated entry point, it isn’t, but because it’s the one that relies on human behaviour, and human behaviour is consistently the hardest security control to enforce.
An endpoint, in security terms, is any device that connects to your network: laptops, desktops, phones, tablets, and increasingly, smart devices in the office. Each one is a potential door. Each one needs to be managed.
Email security — the essential layer:
- Anti-phishing and email filtering: Business-grade email platforms (Microsoft 365, Google Workspace) include built-in security features that need to be actively configured; they don’t protect you out of the box. Consider dedicated email security tools like Proofpoint or Mimecast for higher-risk environments.
- DMARC, DKIM, and SPF records: These DNS configurations prevent attackers from spoofing your domain to send phishing emails that look like they are from your company. Your managed service provider or IT staff can implement these in a matter of hours.
- Business Email Compromise (BEC) protection: Configure your email system to flag external emails that impersonate internal senders or suppliers. Set up approval workflows for any wire transfer or payment requests that arrive via email.
Endpoint protection — beyond consumer antivirus:
- Endpoint Detection and Response (EDR): Modern EDR tools don’t just detect malware; they monitor system behaviour in real time and can isolate an infected device before an attack spreads. Consumer antivirus products are not adequate for business environments.
- Device encryption: Enable full-disk encryption on all company laptops (BitLocker on Windows, FileVault on Mac). If a device is lost or stolen, encrypted data is inaccessible without the key.
- Mobile Device Management (MDM): If employees access company data on phones or tablets, an MDM solution lets you enforce security policies, remotely wipe lost devices, and ensure apps are up to date.
- Patching and update management: Unpatched software is one of the most exploited attack surfaces in cybersecurity. Establish a policy: critical patches applied within 24–72 hours, standard updates within two weeks.
The human layer — training that actually works:
Security awareness training is essential, but most of it doesn’t work because it’s treated as a compliance exercise rather than a behaviour change program. Annual all-hands training produces annual compliance, not daily vigilance.
What works: regular, short, scenario-based training combined with simulated phishing tests. When employees actually click a simulated phishing link, they get immediate, contextual feedback — and that moment of recognition is far more effective than any slide deck.
STEP 5: Build Your Backup & Recovery Foundation (Ransomware Defence)
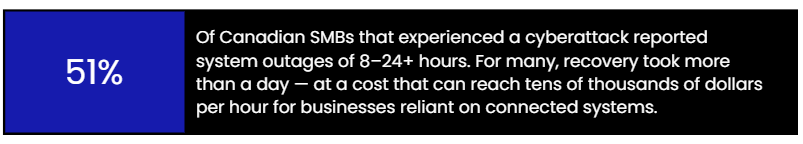
Ransomware is the dominant cyberthreat facing Canadian businesses. The mechanics are straightforward and brutal: malware encrypts your files, attackers demand payment for the decryption key, and your business grinds to a halt until you pay or recover.
In 2024, two-thirds of Canadian small businesses that experienced a ransomware attack paid the ransom. Most of them paid because they had no alternative — no clean backups to restore from, no recovery plan to execute.
Your backup strategy is your ransomware strategy. There is no substitute. If you have clean, tested, immutable backups, a ransomware attack becomes a painful but survivable incident. If you don’t, you’re paying the ransom or rebuilding from scratch.
The 3-2-1 Backup Rule:
• 3 copies of your data
• 2 copies stored on different media types (e.g., internal drive and cloud)
• 1 copy stored completely offsite or in an air-gapped environment (disconnected from your network)
The critical word in that framework is ‘immutable.’ Ransomware has evolved to specifically target backup systems modern ransomware will attempt to encrypt or delete connected backup drives before encrypting your primary files. Ransomware cannot change or remove immutable backups. This is not optional if ransomware is in your risk model and it should be.
STEP 6: Know Your Compliance Obligations (PIPEDA and Beyond)
PIPEDA regulates how businesses in the private sector gather, utilize, and disclose personal data. Under the Breach of Security Safeguards Regulations that took effect in 2018, organizations must:
- Notify Canada’s Office of the Privacy Commissioner of breaches that actually put people at risk of serious harm.
- Notify affected individuals directly when such a breach occurs.
Maintain a record of ALL breaches — even those that don’t meet the reporting threshold — for at least 24 months and make those records available to the OPC on request
Security and privacy compliance has become a commercial gating issue for Canadian startups. Enterprise customers — particularly US-based companies — are now routinely requiring:
- SOC 2 Type II reports: An independent audit of your security controls, availability, and confidentiality practices. Increasingly expected for any SaaS business selling to an enterprise.
- Vendor security questionnaires: Detailed questionnaires covering your security practices, incident response, data handling, and employee training. These can range from 50 to 200 questions.
- Data Processing Agreements (DPAs): Formal contracts governing how you handle customer data, especially for EU-based customers under GDPR or California customers under CCPA.
Security questionnaires are now often sent earlier in the process, sometimes before the product demo. A startup that can’t answer basic security questions competently is losing deals.
STEP 7: Build Your Incident Response Plan Before You Need It
Most businesses plan their response to a cyberattack the same way they plan for a fire: they don’t, because it hasn’t happened yet, and planning for it feels morbid and premature. Then, when it happens, they improvise, and an improvised incident response is almost always more expensive, more damaging, and more chaotic than it needs to be.
An incident response plan is not a complex document. At the SMB level, it doesn’t need to be more than five to ten pages. What it needs to be is specific, tested, and known to the right people before the incident happens
What your incident response plan needs to cover:
- Roles and escalation: Who is notified first when something is suspected? Who makes decisions? Who communicates externally? If you use a managed security partner, their contact details should be the first thing in the plan.
- Contain, don’t wipe: The instinct in an attack is to shut everything down. The right move is to isolate affected systems without destroying the forensic evidence needed to understand what happened and how far it spread. Your plan should include specific containment steps.
- PIPEDA assessment: Your plan should include a decision tree for determining whether a breach triggers mandatory notification under PIPEDA and/or provincial privacy laws. This should involve your legal counsel.
- Communication protocols: Who tells customers? What do you say — and what don’t you say — while an investigation is ongoing? Who speaks to the media? Who handles internal staff communication?
- Insurance notification: Notify your cyber insurance provider early. Many policies have specific notification windows, and late notification can affect coverage.
- Documentation: Everything that happens during an incident should be documented — actions taken, decisions made, timelines, communications sent. This record is essential for insurance claims, regulatory responses, and post-incident learning.
Test it before you need it:
A plan that exists only as a document will fail when it matters. Run a tabletop exercise a discussion-based simulation where your leadership team walks through a mock incident scenario at least once a year. Identify the gaps before the attack does.
Cybersecurity Is a Decision — Not a Delay
Cybersecurity for Canadian businesses is not a problem you solve once and set aside. It’s a posture — an ongoing, evolving set of decisions about what you protect, how you protect it, and what you do when something goes wrong despite your best efforts.
The seven steps are a sequence, each reducing the attack surface. You don’t need to implement all of them right away; just start with the highest-impact step you can execute now. Taking action is better than waiting for a perfect strategy while your systems remain unprotected.
Not sure where your business stands?
We offer a free cybersecurity assessment for Canadian businesses, a no-obligation conversation about where you are, where your gaps are, and what to do first.
Frequently Asked Questions
Canadian businesses must safeguard personal data under PIPEDA by implementing appropriate security controls, such as access restrictions, encryption, monitoring, and breach response procedures. If a breach poses a real risk of significant harm, organizations must notify regulators and affected individuals.
Small businesses are targeted because they often have weaker security controls, limited monitoring, and valuable customer or financial data. Attackers use automated tools to find easy entry points, making smaller companies attractive targets and potential gateways into larger supply chains.
The first step is identifying what you need to protect. Create an inventory of devices, systems, data, and third-party access. Understanding where sensitive information lives and who can access it helps prioritize risks and build effective security controls.
A cybersecurity posture reflects how well an organization can prevent, detect, and respond to threats. It combines policies, technology, and practices. A strong posture reduces risk, enhances resilience, supports compliance, and ensures business continuity in the event of incidents.
Not all startups need SOC 2 or ISO 27001 immediately, but companies selling to enterprise customers often require SOC 2 reports. Compliance demonstrates strong security practices, builds trust, and accelerates sales cycles, making it valuable as the business scales.
Companies should conduct a cybersecurity risk assessment at least annually and whenever major changes occur, such as adopting new systems, expanding operations, or onboarding vendors. Regular reviews help identify emerging threats and ensure security controls remain effective.



