
Less Tech Noise. More Strategic Insights
Join 5000+ Tech leaders & CISOs receiving our deep-dive insights.
Dark Patterns in Subscription Apps: The IT Security Risk
When your finance team flags a SaaS charge that no one remembers approving, it looks like an oversight.
In reality, it often isn’t.
It’s the result of dark patterns, interfaces designed to bypass scrutiny, lock users into subscriptions, and quietly expand access across your environment.
For enterprises managing 50–100+ SaaS tools, this isn’t a UX issue.
It’s a growing governance gap.
“Organizations now underestimate SaaS sprawl by up to 30–40%,” and every unnoticed subscription increases financial leakage, widens your attack surface, and creates compliance exposure—without a single breach.
What Dark Patterns in Subscription Apps Actually Are
User interface elements are deliberately designed to trick users into doing things that are not in their best interests.. While dark patterns are often discussed as a consumer issue, their impact is already visible in subscription ecosystems. Many of these tactics, such as hidden charges, forced continuity, and silent data sharing, have been widely documented as in-app subscription security risks in consumer applications.
In the enterprise context, they mean third-party tool subscriptions that control company data, forgotten accounts, cloud sync, etc.
Deceptive subscription flows are not just a manipulative design. They are an unauthorized data pipeline, an uncontrolled procurement channel, and in many cases, a direct compliance liability.
Approximately 76% of the websites and applications analyzed employed at least one dark pattern, and nearly 67% used multiple dark patterns simultaneously. That is not a fringe problem. That is the majority of the SaaS ecosystem that your employees interact with every day.
The Dark Patterns That Create the Highest Enterprise Security Risk
Not all dark patterns carry the same organizational weight. The following are the patterns most directly relevant to enterprise IT governance, ranked by the security and financial risk they introduce, not by how often they make the news.
1. Roach Motel Tactic: Zombie Accounts and Persistent Access
Roach motel tactics are the most widely recognized dark pattern in subscription apps. signing up is frictionless, but canceling is deliberately engineered to be exhausting. Multi-step cancellation flows, buried settings menus, requirements to call a phone number, or buttons deliberately swapped so “confirm cancel” looks like “upgrade plan” these are features, not bugs.
For an IT manager, the downstream consequence is not just wasted spend. It is zombie accounts.
- When employees cannot easily cancel a subscription, access persists. And persistent, unmonitored access to a third-party application, especially one connected via Single Sign-On or OAuth, is an open door long after the person who signed up has left your organization.
- You cannot enforce Multi-Factor Authentication on an account that IT does not know exists.
- You cannot revoke access during offboarding if the subscription is on a personal card.
- And if that vendor suffers a breach, your organization’s data is in the blast radius.
Example: Amazon Prime was using the roach motel tactic; it took regulatory intervention and 2.5$ billion fine to force a simple cancellation procedure.
If a vendor of that scale was engineering roach motel tactics, assume it is standard practice across much of the SaaS landscape
2. Forced Continuity — The Silent Budget Leak
Forced continuity is what happens when a free trial converts to a paid subscription without meaningful notice or user action. The credit card collected at sign-up is charged automatically. No reminder is sent. The subscription continues until someone actively stops it.
- From a company perspective, when dozens of employees self-subscribe to SaaS tools, it becomes a significant budget leak at scale.
- The average large enterprise manages 476 SaaS renewals annually, nearly two per business day. Without centralized visibility, most of those auto-renewals go unchallenged.
- Gartner estimates that organizations waste up to 25% of their SaaS budget, and forced continuity mechanics.
- This is not an IT operations problem alone. It is a financial governance problem with a deceptive design root cause.
- Beyond budget, forced continuity also means your organization may be paying for a tool it never formally approved and collecting data under a privacy policy the security team has never read.
3. Sneaking and Pre-Selection — The Unauthorized Data Transfer
Sneaking involves the quiet addition of something a user did not explicitly choose: a pre-checked data-sharing checkbox, an automatically granted permission during sign-up, a third-party SDK that starts collecting behavioral data the moment an employee creates an account.
This is where dark patterns in subscription apps cross from financial manipulation into data-privacy territory, and where the risk profile for cybersecurity specialists becomes acute
- Modern SaaS applications rely heavily on third-party Software Development Kits (SDKs) for analytics, payment processing, and subscription management.
- Subscription apps that use pre-selected consent options can lead to data being shared with vendors and embedded SDKs, often without full transparency for either the vendor or the user.
- Under GDPR’s Article 28, if your organization’s data is being processed by a third party on terms that were never properly disclosed or consented to, you carry co-processor liability.
- The FTC’s 2024 findings specifically flagged “sneaking practices” as the most frequently encountered dark pattern type across the global subscription app review.
4. Forced Cloud Sync — Dark Patterns at the Architecture Level
Most dark patterns operate at the interface level. Forced cloud sync is different — it is a deceptive design baked into the product architecture itself, and it is the pattern most directly relevant to enterprise cybersecurity specialists.
In 2024, Postman, one of the most widely used API testing tools in enterprise engineering environments, shifted to a mandatory cloud-sync model. When developers logged in, all their data was automatically uploaded to Postman’s cloud: requests, environment variables, API keys, and access tokens. There was no clear advance warning. There was no true offline alternative.
The security implication was immediate and serious.
- API keys and tokens that had previously lived only on a developer’s local machine were now replicated to a third-party server
- A single breach of the Postman account could expose live credentials to your organization’s production systems.
Forced cloud sync is a dark pattern in the most structurally dangerous form: it does not trick users into clicking the wrong button. It restructures the security perimeter without asking permission.
5. Confirmshaming and False Hierarchy — Employees Manipulated Into Oversharing
Confirmshaming uses guilt-framing to make users feel foolish for exercising their rights. Opt-out buttons labeled “No thanks, I prefer not to save money” or “I don’t want early access” are designed to trigger a compliance response. Users click through the shame rather than asserting their preference.
False hierarchy pairs with this: primary and secondary buttons are given mismatched visual weight, so users click the vendor-preferred option by default, often the option that grants more data permissions, a higher-tier subscription, or auto-enrollment in additional services.
- When new employees encounter these patterns in the SaaS tools they are adopting for work, the result is an organizational data permission set that no IT manager approved and no security review captured.
- This is particularly dangerous in the context of SaaS tools connected to enterprise identity systems via SSO.
- When confirmshaming drives an employee to accept a broader OAuth scope than they intended, that permission persists in your identity infrastructure indefinitely.
From UX Manipulation to Security Incident: Connecting the Dots
The progression from dark pattern to security incident is not hypothetical. It follows a consistent pattern:
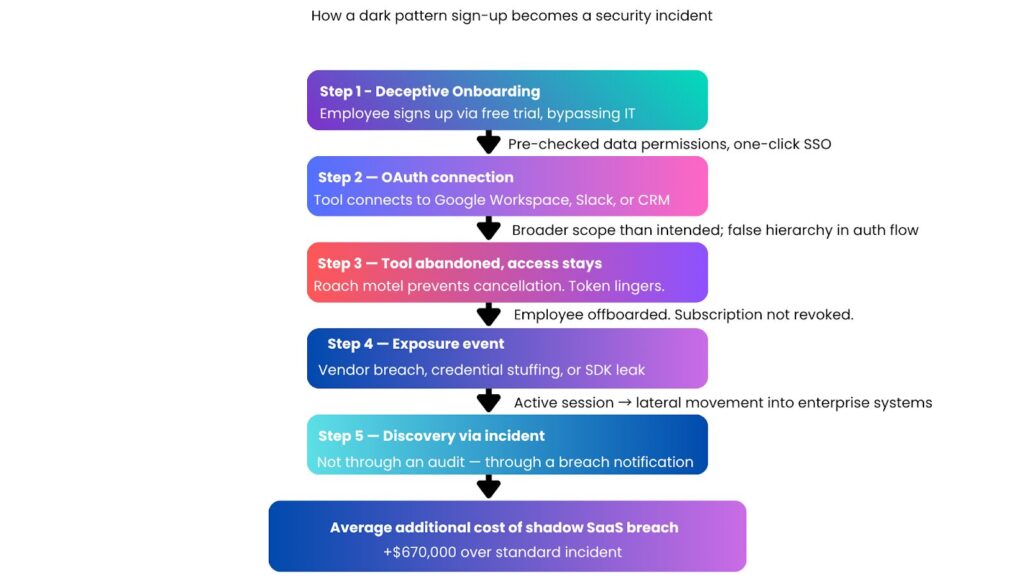
This is the shadow IT pipeline powered by deceptive subscription design. And it is measurably widespread. IBM’s 2025 Cost of Data Breach Report found that 20% of all organizational breaches stemmed from unauthorized AI or SaaS tool use
Building Your Defense: A Three-Pillar Framework for IT and Security Teams
Protecting your organization from dark patterns in subscription apps is not a one-time fix. It is a governance practice built on three interdependent pillars
Pillar 1: Visibility: Know What Is Running in Your Environment
You cannot govern what you cannot see. The first priority is establishing a real-time inventory of every SaaS application active in your environment, including those procured outside of IT
Practical steps:
- Deploy a Cloud Access Security Broker or a dedicated SaaS management platform to continuously discover and classify active applications. Tools like Netskope and Microsoft Defender for Cloud Apps identify shadow IT that traditional monitoring misses.
- Audit OAuth tokens for active apps; revoke those dormant for 90 days with broad scopes.
- Create a SaaS renewal calendar. Large enterprises handle an average of 476 renewals annually, making unmanaged auto-renewals a significant governance risk.

Pillar 2: Policy — Remove the Decision from Individual Employees
Dark patterns exploit individual psychology under time pressure. Policy removes that vulnerability by establishing clear guardrails before an employee encounters a manipulative subscription flow
Practical steps:
- Require IT pre-approval for any SaaS tool before subscription by an employee or business unit. A simple intake form with a 48-hour review SLA is enough. The goal is visibility, not obstruction.
- Vendor Evaluation Checklist:
- – Is the cancellation process documented and phone-free?
- – Are auto-renewal terms disclosed prior to payment?
- – Are data-sharing options opt-in?
- – Does the privacy policy list all third-party SDKs?
- Establish a clear policy on personal credit cards and expense-based SaaS procurement — the most common channel through which dark pattern subscriptions enter enterprise environments without IT oversight
Pillar 3: Compliance Alignment — Treat Dark Patterns as a Regulatory Signal
Regulatory frameworks are increasingly treating dark patterns not as a UX failure but as a legal liability. Your compliance posture needs to reflect that shift.
Practical steps:
- Check your SaaS stack against the EU Digital Services Act, which prohibits dark patterns. Reference specific VLOP rules if applicable.
- Add a dark pattern audit to your vendor security review, covering sign-up, cancellation, consent, data-sharing, and SDK transparency.
- Review your offboarding processes to ensure they include subscription revocation as a defined step, not an afterthought. The persistence of zombie accounts from dark pattern cancellation flows is a documented breach entry point
What This Means for Your Organization
Right Now Dark patterns in subscription apps are not going away. According to global reviews, found that the majority of subscription-based apps and websites use them, and AI-optimized interfaces are making them harder to detect through static audits because the manipulation is now dynamic, tested, and continuously refined.
But the organizational exposure is manageable if it is approached systematically.
The IT manager who can demonstrate leadership, maintain a clear inventory of shadow SaaS, implement a vendor evaluation process that flags deceptive subscription flows, and ensure compliance with DSA and CPRA requirements is not just reducing risk. They are making a case for proactive cybersecurity governance that protects the organization before an incident, not after.
Given that 76% of subscription apps use at least one dark pattern, and that the average enterprise uses more than 100 SaaS tools, the math is straightforward.
Start With a Comprehensive Security Audit
If you are not certain how many SaaS tools in your environment were onboarded through deceptive subscription flows, or which of those tools have active OAuth connections to your core identity infrastructure, or whether your vendor contracts expose your organization to regulatory risk under GDPR and CCPA compliance frameworks, a structured security audit is the right first step.
At Infosprint Technologies, our cybersecurity team works with IT leaders and security specialists to assess the full scope of SaaS-related risk from shadow IT discovery and OAuth token auditing to subscription governance policy design and vendor dark pattern evaluation.
Contact Infosprint Technologies to schedule a comprehensive SaaS security assessment. The exposure from dark patterns in subscription apps is real, measurable, and addressable — but only if you can see it first.readiness assessment and identify your highest-impact opportunities.
Frequently Asked Questions
Dark patterns are user interface design techniques deliberately engineered to manipulate users into taking actions that benefit the vendor rather than the user — including signing up for subscriptions they did not intend, sharing data permissions they did not mean to grant, or being unable to cancel services they want to stop
Dark patterns drive unauthorized SaaS adoption (shadow IT) by making sign-up frictionless while making cancellation deliberately difficult. This results in zombie accounts with persistent access, unauthorized OAuth tokens connected to enterprise identity systems, unmonitored data flows to third-party SDKs, and budget exposure from hidden auto-renewal clauses — all outside IT visibility
Yes. When employees are manipulated into granting broader data permissions than they intended through deceptive subscription flows, the resulting data collection may violate the consent standards required under GDPR and CCPA. Organizations can carry co-processor liability for data collected under these circumstances, even when the dark pattern was implemented by the vendor, not the organization
The three-pillar approach is: Visibility (CASB tools, OAuth audits, SaaS discovery), Policy (IT pre-approval for subscriptions, vendor evaluation checklists, auto-renewal governance), and Compliance Alignment (mapping your SaaS stack to DSA, GDPR, and CPRA dark pattern prohibitions, and incorporating dark pattern audits into vendor security reviews)
Shadow IT refers broadly to any SaaS tool used without IT approval. Dark pattern subscription risk is a specific driver of shadow IT — deceptive onboarding and retention mechanics that actively encourage employees to subscribe individually and make it hard for IT to detect, audit, or offboard those tools. They are related problems, with dark patterns functioning as the supply side engine of shadow IT proliferation
Related Blogs

Missiles, Models & a Pentagon Deal: March 2026
How Retailers Reduce Costs by 40–60% While Improving Customer Experience




