Cybersecurity Awareness Month 2025: Essential Security Tips for Businesses and Individuals

Less Tech Noise. More Strategic Insights
Join 5000+ Tech leaders & CISOs receiving our deep-dive insights.
- What is the importance of Cybersecurity Awareness Month?
- The 2025 Threat Landscape: What’s Changed — and What Hasn’t
- Personal cybersecurity checklist: Fortify your cyber defense
- Cybersecurity best practices for businesses
- CyberTrends to Watch in 2025 and Beyond
- Take Action This Cybersecurity Awareness Month
- FAQs
Cybersecurity isn’t just an IT issue anymore — it’s the backbone of trust in a digital-first world.”
October marks Cybersecurity Awareness Month 2025, but this year, awareness alone won’t cut it. With AI-driven phishing up by 85%, and supply chain attacks targeting even mid-sized businesses, the question isn’t if you’ll be targeted — it’s when.
As AI-powered automation expands and hybrid work blurs perimeters, cybercriminals are evolving faster than ever. From deepfake impersonations to data leaks via unmonitored AI tools, the line between human and machine threats is fading — leaving businesses and individuals equally exposed.
At Infosprint Technologies, 2025 is the year to move from defense to digital resilience. Because in today’s landscape, cybersecurity isn’t about protecting systems — it’s about safeguarding trust, reputation, and continuity.
Let’s explore how this year’s threat landscape has changed and what you can do right now to stay ahead.
What is the importance of Cybersecurity Awareness Month?
The USA first proposed Cybersecurity Awareness Month to raise public awareness of cyberattacks, implement safety measures, deploy new technologies to address them, and promote preventive measures to protect individuals and businesses by educating individuals and companies.
Businesses can leverage Cybersecurity Awareness Month to educate their staff about data security protocols and potential attack vectors. This initiative also fosters the development of cutting-edge technologies to combat cyber threats and raises public awareness of the importance of robust cybersecurity defenses. By promoting education, best practices, and collaboration, We can all contribute to making the internet a safer place.
The 2025 Threat Landscape: What’s Changed — and What Hasn’t
Cyberattacks have grown more sophisticated and automated. The biggest disruptor? Artificial Intelligence — used by both defenders and attackers.
Here’s what’s shaping 2025’s cybersecurity landscape:
- AI-Driven Phishing and Deepfakes:
Cybercriminals now use generative AI to mimic voices, faces, and emails. “CEO fraud” and “vendor payment scams” are nearly indistinguishable from reality.
- Supply Chain & Vendor Risks:
60% of breaches in 2025 stem from third-party vendors with weak security protocols. Businesses are only as secure as their least protected partner.
- Cloud & Edge Vulnerabilities:
As workloads move to multi-cloud and edge environments, misconfigurations and API loopholes remain top attack vectors. - Identity as the New Perimeter:
With hybrid work and remote collaboration, identity management is now your first line of defense. Stolen credentials still fuel most attacks. - AI Tool Misuse (Shadow AI):
Employees using unapproved AI tools risk leaking sensitive corporate data without realizing it. - Skills Gap Widening:
75% of organizations say they can’t find enough skilled cybersecurity talent, forcing them to outsource monitoring and incident response.
- Insider threat or Human error:
According to most cybersecurity experts, human error or insider threats are the most significant and devastating attacks. These cannot be detected by AI algorithms or codes.
Takeaway: Attackers now exploit human behavior, AI loopholes, and supply chain dependencies. Businesses must go beyond firewalls and antivirus — adopting a Zero-Trust, AI-aware security strategy.
Personal cybersecurity checklist: Fortify your cyber defense
Even as businesses harden defenses, individuals remain the easiest targets. In 2025, protecting yourself means anticipating AI-powered deception.
- Use passphrases, not passwords: Choose long, memorable phrases (e.g., MangoTreeRuns@Night).
- Adopt passwordless authentication (like biometrics or passkeys) wherever possible.
- Stay alert for deepfakes: Don’t trust video calls or voice notes requesting urgent action.
- Secure your home network: Update router firmware, enable WPA3, and isolate IoT devices.
- Regularly back up data — ideally to immutable, offline storage.
- Be cautious with AI chatbots or assistants: They can retain and leak sensitive information.
- Review privacy permissions: Delete old accounts and revoke unused app access quarterly.
- Keep devices patched: Outdated browsers, routers, and IoT devices are hacker favorites.
Pro tip:
Create a “Cyber Hygiene Day” once a quarter — review devices, reset passwords, and check your digital footprint. It’s the digital equivalent of changing your smoke detector batteries.
Also, refer to our Mobile Security 101 guide if you want to lock down your phone and home devices, too.
Cybersecurity Best Practices For Businesses
For organizations, the challenge isn’t just preventing breaches — it’s maintaining continuity and trust when they happen. Here’s how businesses can stay secure in 2025:
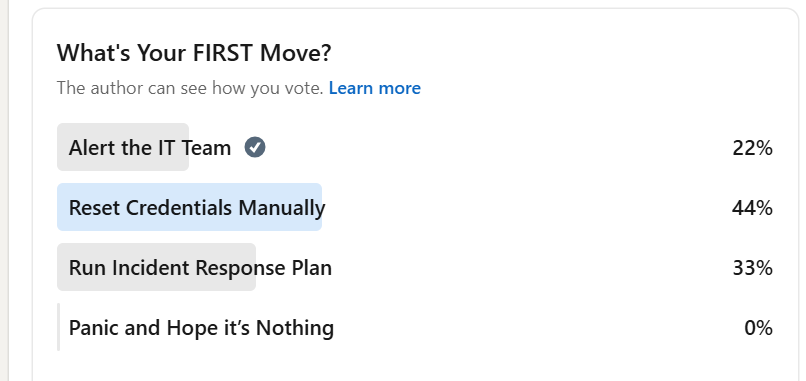
When a cyber threat hits, your team’s first move can make or break your response.
But here’s the catch — not everyone reacts the same way.
Surprising, right? Nearly half of professionals (44%) said they’d reset credentials manually, while only a third would actually run the incident response plan. Just 22% would alert the IT team first.
This isn’t just a stat — it’s a signal.
Even in well-prepared organizations, human instinct often overrides protocol. People tend to act fast rather than act right.
a. Adopt Zero-Trust Architecture
- Assume every user, device, and app is untrusted until verified.
- Implement continuous authentication and micro-segmentation to limit access and reduce lateral movement.
b. Secure the Supply Chain
- Audit third-party vendors for compliance and readiness to respond.
- Use continuous monitoring tools and risk-scoring dashboards to identify weak links early.
c. Strengthen Identity and Access Management (IAM)
- Centralize IAM systems and enforce least-privilege access.
- Introduce just-in-time credentials to limit exposure windows.
d. Manage Shadow AI Risks
- Set clear guidelines for employee use of AI tools like ChatGPT or Copilot.
Integrate AI governance policies into your data protection framework.
e. Upgrade from Detection to Response
- Adopt Managed Detection and Response (MDR) or Security Operations Center (SOC) as a Service to offset internal skill shortages.
- Outsourced 24/7 monitoring reduces response time and improves containment.
f. Train Beyond Phishing
- Replace generic training with real-world simulation — deepfake videos, fake invoices, vendor scams, and educate employees on how social engineering gets more sophisticated.
- Behavioral awareness is now as critical as technology.
g. Build a Culture of Cyber Resilience
- Cybersecurity is no longer just IT’s job. Leadership teams must align cyber investments with business strategy.
- Regular tabletop exercises and incident response drills build preparedness and confidence.
CyberTrends to Watch in 2025 and Beyond
The next wave of cybersecurity is already here. Innovative businesses are preparing today for the threats of tomorrow:
- Post-Quantum Cryptography: Start planning migration strategies for quantum-safe encryption.
See our deep dive on quantum cyber threats and how to evaluate your encryption readiness.
- AI Governance Frameworks: Balance AI adoption with compliance and ethical use.
- Consolidation of Security Stacks: Simplify multiple tools into unified platforms to reduce complexity.
- Continuous Threat Intelligence: Move from static risk audits to real-time risk scoring.
- Cyber Insurance Evolution: Expect insurers to demand stricter compliance before coverage.
Don’t just secure your systems — secure your adaptability. The faster your organization detects, learns, and recovers, the stronger your long-term resilience.
Take Action This Cybersecurity Awareness Month
Cybersecurity Awareness Month is more than an annual reminder — it’s your opportunity to reset, educate, and upgrade.
Whether you’re an individual safeguarding your personal identity or an enterprise protecting sensitive data, the time to act is now.
At Infosprint Technologies, we help businesses transform cybersecurity from a compliance checkbox into a competitive advantage — through:
- VAPT (Vulnerability Assessment & Penetration Testing)
- GRC (Governance, Risk & Compliance) solutions
- Cloud security optimization and audits
- AI governance and cyber risk consulting
Explore our cybersecurity solutions to understand how we can assist you.
Ready to Strengthen Your Cyber Resilience?
Protecting your organization in 2025 starts with a single step.
Book a free 30-minute Cyber Readiness Consultation with Infosprint Technologies.
We’ll help you assess risks, build resilience, and secure your business against next-generation threats.
Or subscribe to our Cybersecurity Digest to receive monthly updates, actionable tips, and industry insights straight to your inbox.
Frequently Asked Questions
It’s the annual October campaign to raise digital safety awareness and to act on emerging cyber risks.
AI-driven phishing, supply-chain attacks, identity-first threats, and hybrid/edge exposures are now more dominant.
Use passphrases or passwordless auth, keep devices and routers updated, be alert to deepfakes, and separate home/work networks.
Adopt zero-trust, secure vendor/supply-chain, strengthen IAM, train beyond standard phishing, and integrate continuous threat-intelligence and MDR.
Post-quantum crypto, AI governance, security stack consolidation, continuous monitoring, and evolving cyber-insurance demands.
Related Posts
Top 10 Cloud Computing Technologies to Look Out for in 2025

Consistent Diagnosis: The Cornerstone of Modern Healthcare




