
Less Tech Noise. More Strategic Insights
Join 5000+ Tech leaders & CISOs receiving our deep-dive insights.
Sovereign Cloud: Why Data Sovereignty Is Becoming a Strategic Business Priority
Your company’s data might be stored in Canada, Singapore, UAE or the US.
Is that data actually under your country’s control?
In today’s global cloud ecosystem, the answer is often no.
Even when organizations carefully select in-region data centers, the legal jurisdiction governing that data may still be tied to the cloud provider’s headquarters. Laws like the U.S. CLOUD Act allow authorities to request data from American cloud companies—even if the data physically resides in another country.
For enterprises operating in regulated industries or handling sensitive intellectual property, this creates a complex risk landscape. As a result, organizations worldwide are beginning to rethink a core assumption of the cloud era: who really controls data.
This shift is driving the rapid rise of the sovereign cloud.
But sovereign cloud is not simply another deployment option. It signifies a major change in the way organizations approach control, compliance, and digital infrastructure.
At Infosprint Technologies, we see this shift as the start of a broader conversation around how companies design cloud environments that balance scalability, compliance, and long-term data control.
What Is a Sovereign Cloud?
At its core, sovereign cloud is about ensuring that data remains fully governed under the legal and operational control of a specific country.
A sovereign cloud environment ensures that data is:
- Stored within national borders
- Processed within that jurisdiction
- Governed only by local laws and regulations
You can think of a sovereign cloud as a digitally fortified vault.
The infrastructure may still use cloud technologies, but only the laws of that country hold the key to accessing the data inside.
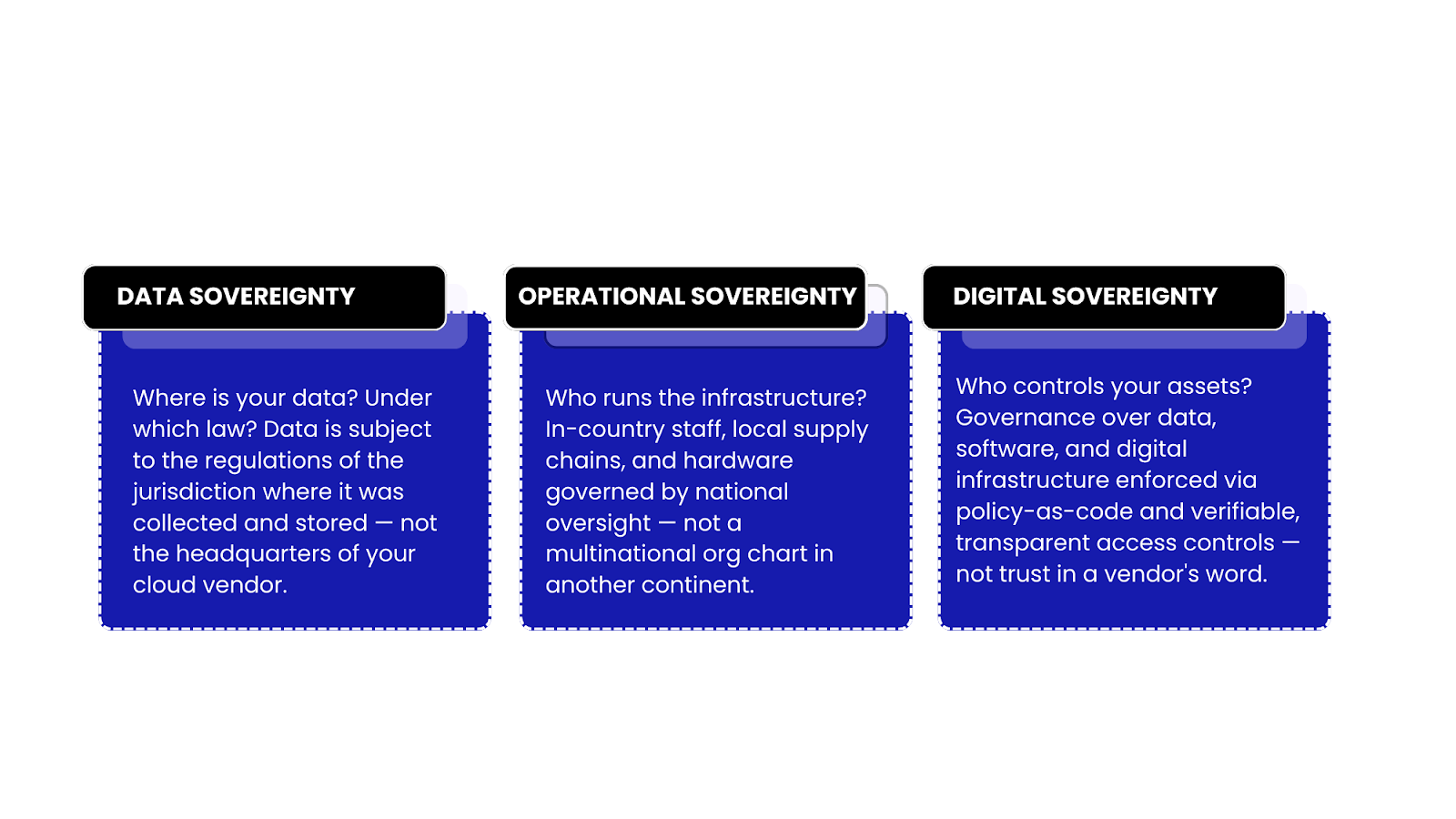
This concept is built on three pillars.
The sovereign cloud market reached $103.97 billion in 2025 and is projected to grow at a 23.9% CAGR, with analysts forecasting the market could exceed $242 billion within the next few years.
“Digital sovereignty is not just a regulatory requirement; it’s a strategic advantage. By unifying public, private, and sovereign clouds, organisations can adapt faster, optimise performance, and access best-in-class services.”
— Olivera Majdandzic, Partner, Cloud Transformation, PwC France & Maghreb
Sovereign Cloud vs Traditional Public Cloud
Traditional hyperscale cloud platforms are designed primarily for scalability, elasticity, and global distribution.
The sovereign cloud introduces a different priority: control and jurisdiction.
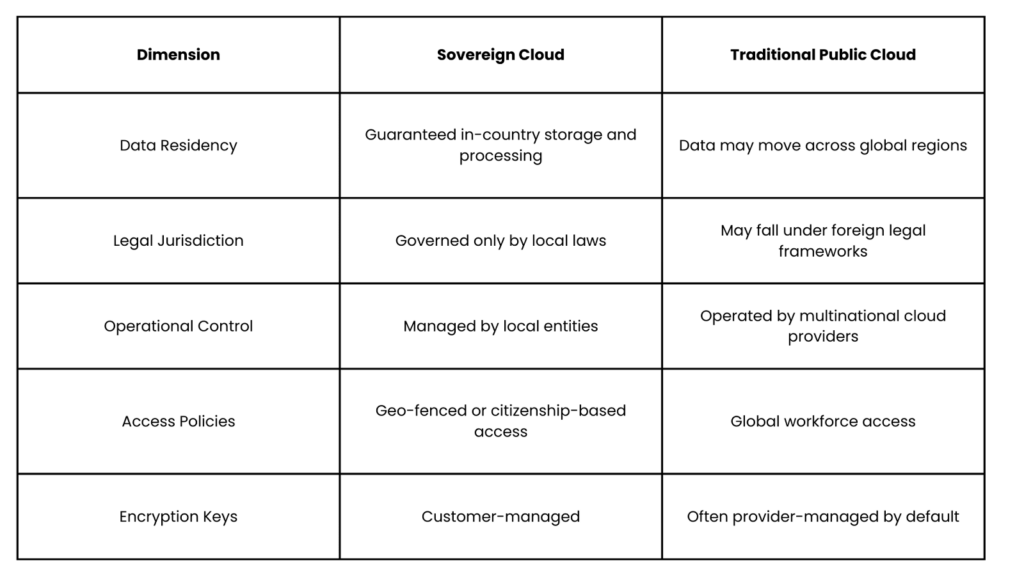
This difference may appear subtle on paper, but it has major implications for security, compliance, and national regulatory exposure.
Why Sovereign Cloud Is Trending Now
Several global trends are converging to accelerate the adoption of sovereign cloud infrastructure.
1. Geopolitical Fragmentation
Global technology infrastructure is no longer politically neutral. Trade tensions, sanctions, and geopolitical conflicts are forcing organizations to reconsider reliance on foreign digital infrastructure.
In fact, 61% of CIOs in Western Europe say geopolitical risks now influence their cloud provider decisions. For boards and executives, cloud strategy has quietly become part of the geopolitical risk management landscape
2. The CLOUD Act and Extraterritorial Data Access
One of the least understood risks in enterprise cloud strategy is extraterritorial legal authority.
The U.S. CLOUD Act allows American authorities to request data from U.S.-based cloud providers—even when the data resides in servers outside the United States.
This means:
- Data stored in European or Asian regions
- Hosted by a U.S.-headquartered provider
may still be legally accessible through U.S. legal frameworks.
For organizations handling sensitive data, this creates a jurisdictional gray area.
3. Regulatory Acceleration
Around the world, regulators are tightening data governance requirements.
Examples include:
- GDPR in Europe
- NIS2 Directive for cybersecurity compliance
- DORA for financial sector resilience
- EU Cybersecurity Certification Scheme (EUCS)
- India’s Digital Personal Data Protection Act (DPDP)
- China’s Cybersecurity Law
These frameworks increasingly require data localization, operational transparency, and auditable compliance controls.
In many cases, traditional public cloud configurations struggle to satisfy these requirements.
4. The AI Sovereignty Challenge
The rapid rise of generative AI has created a new problem for enterprises.
Organizations want to deploy AI systems trained on proprietary data—but sending that data into external AI platforms introduces serious risks.
These include:
- intellectual property leakage
- regulatory violations
- loss of competitive advantage
As a result, many enterprises now require AI inference and training environments that remain within national boundaries.
Sovereign cloud provides a credible infrastructure foundation for these workloads.
5. Cybersecurity Economics Are Changing
The average global cost of a data breach now exceeds $4.4 million.
Ransomware alone affects 59% of businesses worldwide.
For regulated industries like healthcare, finance, and government, the real cost often includes:
• regulatory penalties
• legal exposure
• reputational damage
Sovereign architectures cannot eliminate cyber threats — but they can significantly reduce the blast radius of an incident.
Not sure where your data really stands?
Many organizations assume their data is compliant simply because it sits in a regional data center. In reality, legal jurisdiction, provider governance, and encryption control can expose hidden sovereignty risks.
Don’t guess—audit. Download our “Sovereign Cloud Readiness Scorecard” to map your current infrastructure against the 5 critical compliance pillars we’ve outlined below.
The Hidden Business Problems Sovereign Cloud Solves
What makes sovereign cloud interesting is that many organizations already experience the problems it addresses.
They simply haven’t connected those challenges to sovereignty yet.
Here are some of the most common ones.
1) AI Projects That Can’t Move Beyond Pilot
Many companies experiment with AI but struggle to move projects into production.
The reason often isn’t technical; it’s legal approval.
Compliance teams frequently block AI deployments because sensitive datasets would need to leave national or organizational boundaries.
Sovereign AI environments solve this by allowing AI workloads to run entirely within controlled jurisdictional environments.
2) Vendor Lock-In Concerns
Enterprises migrating workloads between cloud providers often discover that critical governance components, such as identity systems, encryption keys, and audit logs, are tightly integrated with the original provider.
Moving workloads can require rebuilding governance frameworks from scratch.
Sovereign cloud architectures often emphasize customer-managed encryption keys and open APIs, improving portability and reducing lock-in.
3) Escalating Compliance Costs
Regulators no longer accept simple policy documentation.
They increasingly demand continuous evidence of compliance, including:
- real-time audit trails
- automated reporting
- proof of policy enforcement
Manual compliance processes are becoming unsustainable at scale. Sovereign cloud environments often embed policy-as-code and automated compliance monitoring, reducing the operational burden.
4) Third-Party and Supply Chain Risk
Cloud providers rely on complex global supply chains.
Infrastructure maintenance, updates, and access privileges may involve personnel and systems across multiple jurisdictions.
This creates blind spots in third-party risk management.
Operational sovereignty requirements address this by enforcing:
- local infrastructure management
- verified personnel access
- auditable supply chain controls
5) Rising Cloud Costs
Unpredictable pricing models—especially for AI workloads—are driving frustration among finance and infrastructure teams.
Data egress charges, token-based billing, and premium services can make long-term cost forecasting difficult.
Sovereign cloud models often introduce dedicated infrastructure and negotiated pricing structures, improving cost predictability.
6) Data Breach Liability
The average cost of a data breach reached $4.4 million in 2025, and penalties can be significantly higher for regulated industries.
When data crosses multiple jurisdictions, breach investigations become even more complex.
Keeping data within defined legal boundaries—with strict access controls and customer-managed encryption—can significantly reduce exposure.
The Strategic Shift in Enterprise Cloud
Cloud strategy is no longer a simple decision between public and private clouds.
Today’s enterprise infrastructure is becoming multi-layered and jurisdiction-aware.
A common model emerging among mature organizations looks like this:
- General workloads remain on hyperscale cloud platforms for scale and flexibility.
- Sensitive or regulated workloads move to sovereign environments.
- Governance frameworks unify visibility across both environments.
Research shows that only 18% of organizations now rely on a single cloud environment, while most enterprises operate multi-cloud strategies.
In practice, sovereignty is rarely an all-or-nothing proposition.
Instead, organizations adopt different levels of sovereignty depending on workload sensitivity.
This spectrum may range from:
- Public cloud with sovereignty controls
- In-country sovereign regions
- Dedicated sovereign cloud environments
- Fully private sovereign infrastructure
- Air-gapped sovereign systems for critical infrastructure
The key is aligning workload sensitivity with the appropriate sovereignty level.
Building Sovereignty Into Cloud Architecture
For technology teams, sovereign cloud introduces several architectural considerations.
Some of the most important include:
Sovereignty-by-design
Compliance must be embedded into infrastructure design rather than applied after deployment.
Customer-managed encryption keys
Organizations increasingly retain full control over encryption keys rather than relying on provider-managed systems.
Policy-as-code governance
Automated enforcement ensures data residency, access policies, and compliance controls remain consistent across environments.
Multi-cloud portability
Open standards and interoperable APIs become critical to prevent long-term vendor lock-in.
These architectural practices help ensure sovereignty is not just a policy objective—but a technical reality.
Is Your Cloud Strategy Ready for the Sovereignty Era?
The rules governing cloud infrastructure are changing quickly.
Trade laws, data protection regulations, and AI governance frameworks are reshaping how organizations design their digital infrastructure.
For many companies, the key question is no longer whether sovereign cloud will matter.
It is how soon their cloud strategy needs to adapt.
A good starting point is simple:
- Map where your critical data lives
- Identify workloads with regulatory exposure
- Evaluate whether your current cloud architecture supports sovereignty requirements
Because the next compliance audit, regulatory change, or geopolitical shift may arrive faster than expected.
And when it does, control over your data may become your most important infrastructure decision.
Contact our team to start the conversation. We’ll help assess your cloud environment and identify sovereignty risks.
Frequently Asked Questions
A sovereign cloud is a cloud environment where data is stored, processed, and governed within a specific country’s legal jurisdiction.
Organizations are adopting sovereign cloud to manage data sovereignty requirements, reduce legal exposure from foreign jurisdictions, and comply with regional regulations.
Public cloud prioritizes scalability and global infrastructure, while sovereign cloud focuses on jurisdictional control, local compliance, and restricted access.
Yes. The U.S. CLOUD Act allows authorities to request data from U.S.-based cloud providers even when the data is stored outside the country
Industries handling regulated or sensitive data—such as finance, healthcare, government, and defense—are the most likely to require sovereign cloud environments.
Related Blogs

February’s Tech Signals Shaping Cloud, AI, and Security Decisions

Cybersecurity 2026: Identity, AI & Security at Machine Speed




