Less Tech Noise. More Strategic Insights
Join 5000+ Tech leaders & CISOs receiving our deep-dive insights.
Holiday Payment Fraud: Weak Links in APIs & Gateways
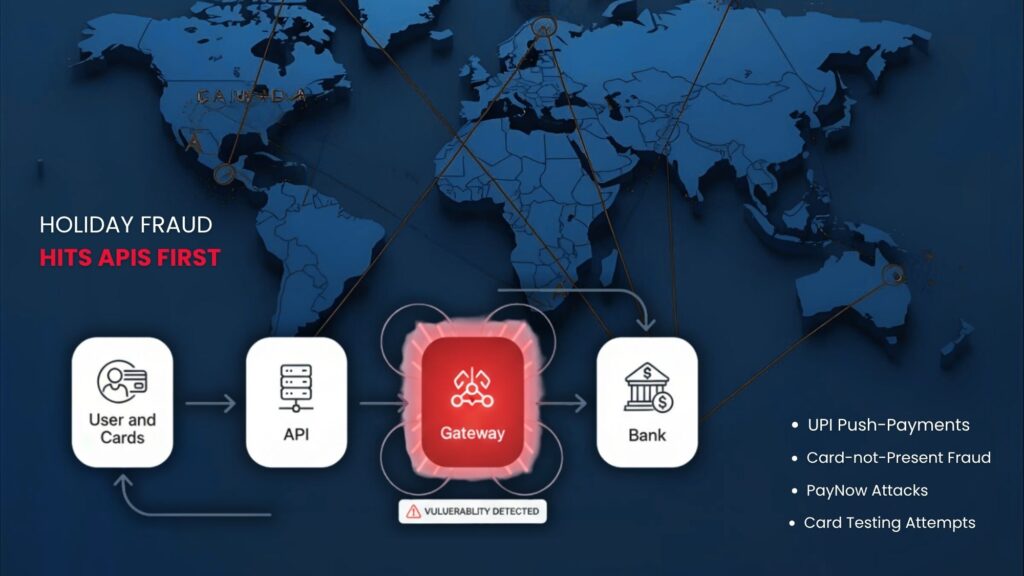
Payment fraud spikes globally — and the weakest links aren’t customers.
They’re your APIs and payment gateways.
During festive seasons like Black Friday and Diwali, payment fraud is rising 3 to 5 times faster than transaction volume. Criminals exploit vulnerabilities in APIs and payment systems, turning minor flaws into significant risks. And despite the rise of digital payments, many merchants underestimate the increased risk of fraud during holiday shopping surges. Understanding this shift is crucial before analyzing specific attack vectors.
In this blog, deep dive into holiday season vulnerabilities, identify high-risk regions, and outline steps businesses can take to protect their payment systems.
With Infosprint’s expertise in API security and VAPT, know where attackers target before the festive surge.
Fraud Tactics That Peak During Holiday Seasons
- Card Testing Attacks (USA/Canada focus): Bots test thousands of low-value transactions via APIs until they find valid credit card numbers.
- Account Takeover (Singapore–USA focus): Attackers exploit weak password resets or intercepted OTPs.
- Instant Payment Manipulation (Singapore/India focus): Real-time payment systems leave little room for dispute reversal.
- Refund & Chargeback Abuse: Holiday return seasons are perfect for fake disputes.
- API Injection & Payload Tampering: Attackers alter transaction amounts, merchant IDs, or currency codes.
Increased pressures not only raise the number of fraud cases but also reveal weaknesses in payment systems. Under extreme load, minor misconfigurations or outdated integrations can become significant entry points for attackers.
Why Online Fraud Spikes During the Holiday Season
Holiday sales create the perfect storm for fraudsters:
- Transaction volumes increase 3–5x, overwhelming fraud systems.
- Merchants relax friction controls to reduce cart abandonment.
- New seasonal staff lack fraud-awareness training.
- Customers shop across unfamiliar merchants, increasing phishing and spoofing risks.
These conditions impact every region:
- USA: High credit-card usage + digital wallets = more CNP fraud
- Canada: Contactless + e-commerce growth = gateway manipulation attacks
- Singapore: A surge in digital wallets + PayNow/QR payments = API & real-time fraud
- India: UPI dominance = increased APP fraud (authorized push payment fraud)
At Infosprint, we observed a sharp increase in spear-phishing attempts, business email compromise (BEC) scams, API misconfigurations, and integration flaws across the manufacturing, pharmaceutical, e-commerce, and IT/ITES sectors during festive sale periods.
No matter the market, the core problem is the same:
Attackers target the technology that connects payments — specifically, the APIs and gateways.
In PwC’s April 2025 Payments Fraud Report, UPI and real-time payment systems continue to experience sharp fraud growth during high-volume periods.
What Hackers Really Target During Holiday Sales
During the holiday surge, attackers target vulnerabilities within payment pipelines. The weakest links aren’t customer mistakes; they’re the overlooked API, gateway, and authentication layers, which are strained under extreme traffic.
1) Weak Authentication
APIs that trust static or insufficiently protected credentials (such as API keys, long-lived tokens, or missing mutual TLS) allow attackers to impersonate services or users.
How attackers exploit it:
- Leaked API keys posted accidentally to public repos or extracted from compromised developer machines are used to call sensitive endpoints (refunds, payout initiation).
- Long-lived tokens let attackers maintain access for months without reauthorization.
- No mTLS allows man-in-the-middle (MitM) for server-to-server calls inside cloud networks.
- No IP whitelisting allows requests from attacker infrastructure to reach internal callback endpoints.
Mitigations:
- Short-lived tokens (OAuth 2.0 access tokens with refresh tokens). Tokens should expire in minutes/hours, not months.
- Rotate keys automatically and revoke unused keys. Implement automated alerts when new keys are provisioned.
To understand the exact vulnerabilities attackers exploit inside API flows, explore our detailed guide on API security testing and VAPT for payment endpoints.
2) Replay Attacks
An attacker captures a legitimate payment request (or callback) and resends (“replays”) the same request to induce duplicate transactions or bypass checks.
How attackers exploit it:
- An intercepted callback from the payment gateway is replayed to mark a transaction “succeeded” twice (duplicate credit).
- Replaying an authenticated payment initiation when the merchant’s webhook doesn’t verify timestamps or signatures.
Mitigations:
- Unique nonces + timestamps: require nonce and timestamp fields; reject if timestamp older than threshold (e.g., 30s) or once seen before.
- Signed payloads: HMAC-SHA256 signature over canonicalized payload + timestamp; verify server-side.
3) Logic Flaws in Payment Flows
Business-logic weaknesses in how you validate, authorize, or process payments, not just technical holes that allow attackers to manipulate transactions.
How attackers exploit it :
- Amount manipulation: The frontend accepts one amount; the attacker tampers with the request to charge a lower/higher amount, or changes the currency code to exploit FX rounding.
- Header injection: Attacker injects headers to trigger a fallback path in your routing logic (e.g., X-Forwarded-For spoofing to bypass geofencing).
- Skipping risk-scoring: During traffic surges, teams may temporarily bypass heavy risk checks to expedite checkout; attackers time their attacks to coincide with these bypass windows.
Mitigations:
- Canonicalize and server-validate all monetary fields. Never trust client-supplied totals; recalculate on the server using order line items and merchant pricing logic.
- Strict header validation: strip unknown headers at ingress; only accept trusted proxies’ headers.
4) Unthrottled Endpoints (Card-Testing & Rate Abuse)
Endpoints that accept high request volumes without rate limiting or anomaly detection, enabling automated card-testing or credential-stuffing attacks.
How attackers exploit it:
- Card testing: Attackers submit thousands of micro-charges ($0.50–$1.00) to detect valid card numbers through API endpoints that accept micro-transactions.
- Credential stuffing: Using breached username/password lists against login or wallet-roaming APIs.
- API flooding: High volume of requests to flood fraud engines and mask fraudulent transactions among regular traffic.
Our VAPT teams frequently uncover foundational weaknesses—such as unnecessary open ports, unsanitised data flows between app and database layers, and potentially unwanted applications (PUA) on user systems.
Mitigations:
- Rate limiting & quota per entity: apply limits per API key, per IP, per user account, and per payment instrument (BIN).
- Progressive throttling & challenge escalation: escalate from soft throttling → CAPTCHA or step-up authentication → block.
Technical flaws and overlapping responsibilities between merchants and payment processors create security gaps during holiday sales, highlighting the importance of shared responsibility in gateway security.
The Challenge of Shared Responsibility Between Merchants and Payment Processors
One of the most significant issues is ambiguity in responsibility:
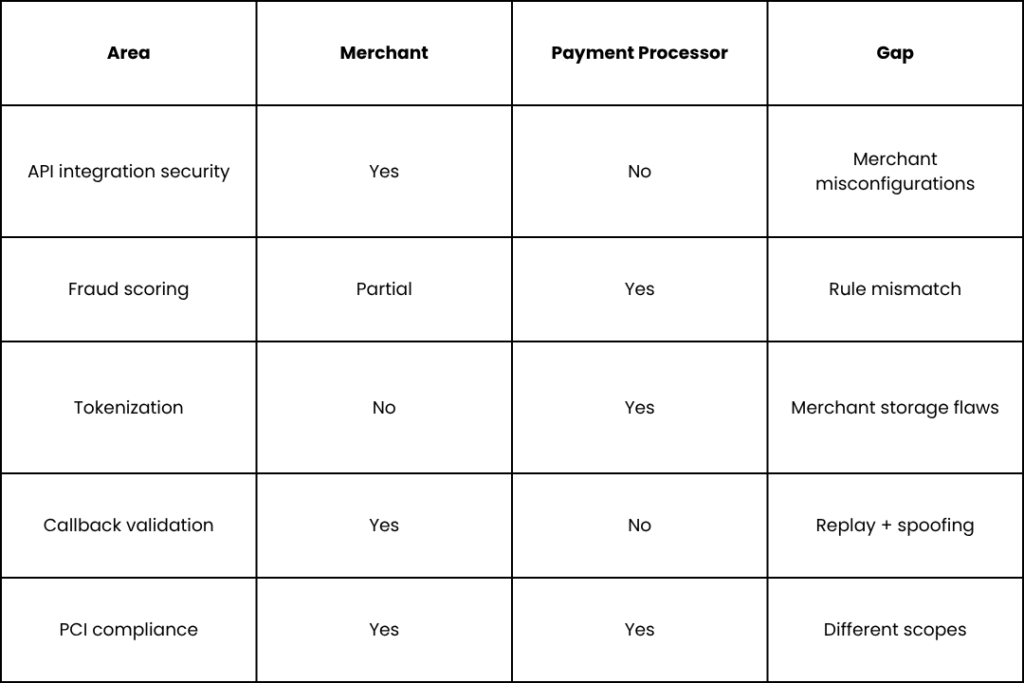
Why This Becomes Critical During Festivals
- Merchants loosen fraud rules for faster checkout.
- Gateways operate at peak capacity, causing delays in dynamic updates.
- Processors expect merchants to secure their endpoints, while merchants often assume the processor handles this task.
This gap becomes the attack surface.
Attackers exploit the “who owns what?” confusion, especially in regions with multiple payment layers, like:
- UPI apps + PSPs + banks (India)
- Wallet + gateway + card network (Singapore, USA)
- Merchant + acquirer + issuer + Interac (Canada)
Many merchants fail compliance checks due to configuration gaps — a problem that can be solved with gap analysis services for payment compliance.
How Global Businesses Can Strengthen APIs & Gateways
Businesses should conduct pre-season security audits and VAPT services for API and gateway security to uncover flaws before fraudsters exploit them.
1. Deploy Multi-Layered Fraud Monitoring
Holiday fraud cannot be detected with a single tool. Businesses need multiple layers working together — rule-based, behavioral, velocity, device fingerprinting, and ML-based scoring. Real-time analytics help identify patterns such as unusual spending spikes, rapid-fire micro-transactions, abnormal device behavior, or mismatched geolocation.
This is especially critical for global merchants, as fraud signatures vary by region and payment method (e.g., UPI in India, PayNow in Singapore, CNP in the US/Canada).
2. Use Strong API Authentication
Weak API authentication is the #1 way attackers compromise payment systems during festive surges. Strengthen your controls by:
- Rotate API keys regularly to ensure that exposed or leaked keys become useless quickly.
- Enforcing token expiration with OAuth 2.0 short-lived tokens to eliminate long-term misuse.
- Implementing mTLS to ensure both client and server authenticate each other, blocking man-in-the-middle attacks.
- Adding IP/domain whitelisting, so only approved servers and networks can reach sensitive payment endpoints.
Together, these measures make credential theft and API spoofing significantly harder.
3. Validate All Webhooks
Payment gateways rely heavily on callbacks and webhooks for status updates — and these are prime targets for exploitation. Strengthen webhook security by:
- Verifying cryptographic signatures so only genuine gateway messages are accepted.
- Checking timestamps to prevent attackers from replaying older webhook payloads.
- Implementing replay-prevention logic, such as storing unique webhook IDs or nonces to block duplicates.
Without validation, attackers can spoof “payment success” calls or replay refunds, making webhook hardening essential.
4. Harden Payment Gateways with Region-Specific Controls
Different regions use different payment methods, so the fraud-prevention strategy must match local attack patterns:
- USA/Canada → Enable 3DS 2.0
Reduces CNP fraud by verifying the customer using risk-based authentication. - Singapore → Add biometric or step-up authentication
Wallets like GrabPay, PayLah!, and Google Pay support biometric verification and multi-factor authentication for high-risk transactions. - India → Use UPI SafePay and device-binding
These prevent UPI fraud by requiring device-level verification and blocking unauthorized UPI intent flows.
A “one-size-fits-all” strategy doesn’t work for global payment ecosystems.
5. Stress-Test Your Systems
High-traffic sale periods often expose hidden performance issues that turn into security gaps (timeouts, fallback flows, skipped checks).
Before the season begins:
- Simulate 5x normal traffic
- Test for queue overflow and timeout failures
- Validate that fraud rules still execute under high load
- Ensure payment retry logic doesn’t accidentally bypass controls
Load testing ensures your gateway, API endpoints, and fraud engines remain stable under extreme conditions.
6. Monitor Cross-Border Transactions Separately
Fraud patterns differ significantly across regions due to payment method preferences, regulatory differences, and cultural usage patterns.
Global businesses should:
- Create region-specific fraud rules (e.g., BIN filters for US/Canada, device-binding anomalies for India, PayNow anomalies for Singapore).
- Maintain separate velocity limits per region or payment method.
- Utilize geolocation and IP reputation to identify suspicious cross-border transactions.
This prevents attackers from abusing “weaker” regions in your global payment flow.
Infosprint’s API Hardening Model
As part of our security assessments, Infosprint recommends the following API Hardening Model to reduce real-world fraud and misconfiguration risks:
- Static and Dynamic Analysis of the source code
- Intrusion Detection Systems (IDS) for real-time anomaly alerts
- Regular Security Updates across servers, libraries, and gateways
- Automated Alerts for API misuse, replay anomalies, and credential abuse
- Secure API Design & Implementation aligned with OWASP and PCI-DSS
- Zero Trust Model enforced across all services, users, and integrations
The Global Risk Outlook: 2025 and Beyond
As payment methods converge globally, so do attack patterns.
- APIs will remain the #1 fraud attack vector
- Real-time payments (UPI, PayNow, FedNow) will be the fastest-growing fraud target
- The increasing use of digital wallets in the USA, Canada, and Singapore will likely lead to an increase in token detokenization fraud.
- AI-driven fraud bots are expected to increase card testing and account takeover attacks.
- Fake payment pages are one of the fastest-growing threats during seasonal sales, as seen in recent festive sale scams and attacks on fake shopping sites.
Merchants must stop viewing payment fraud as a seasonal problem.
It’s a year-round challenge in API and gateway security.
Don’t wait until peak season to discover a weak link.
Strengthen your payment pipeline now with a festive-season API health check with Infosprint’s VAPT experts.
Frequently Asked Questions
Payment gateways are most commonly compromised through weak API authentication, replay attacks, unvalidated webhooks, and card-testing bots that blend into peak traffic. During holiday surges, fraud systems are overloaded and attackers exploit misconfigurations, skipped validation steps, or fallback payment flows.
Merchants should implement multi-layered fraud monitoring, validate all gateway callbacks, rotate API keys, enable 3D Secure or biometric authentication, and conduct stress tests on their systems ahead of peak traffic. These steps ensure payment flows remain secure even when transaction volumes spike.
During festive sales, APIs handle massive surges in requests, making flaws more visible. Weak authentication, long-lived tokens, unthrottled endpoints, and incorrect payload validation create easy entry points for attackers. Because APIs sit between the merchant and gateway, a single flaw can compromise the entire payment chain.
PayNow and wallet-based fraud can arise from replay attacks and push-payment manipulation. Other threats include card-not-present fraud, chargebacks, account takeover, and large-scale card-testing attacks. UPI-based fraud involves app overlays, intent-flow manipulation, and QR hijacking. Each region’s preferred payment method reveals distinct vulnerabilities during festivals.
Merchants should deploy OAuth 2.0, enforce mTLS, rotate tokens, validate webhook signatures, block replay attempts, and implement rate limits at the card BIN, IP, and API key levels. These controls prevent attackers from exploiting API blind spots when traffic is at its highest.
Related Blogs

Black Friday 2025 – 5 Proven Strategies to Gain Control of Traffic Spikes
How Predictive Autoscaling Helps You Survive (and Win) the 2025 Holiday Surges